It appeals to my sense of humour that removing vCenter SSO from vRA has allowed for the introduction of real single sign on in vRA7.
This post isn’t revolutionary, in fact you can read how to set this up in our product documentation. Consider this a post to spread the word that single sign on is doable. Since you’ve read this far, I’ll give you an overview of the steps.
Note: All of these steps are performed from within the context of Administration > Directories Management.
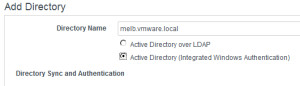
- Go to the Directories tab and ensure that your directory is set to use Integrated Windows Authentication. If it isn’t, just delete it and recreate. Roles won’t be lost, but you will need to wait for users and groups to sync again.
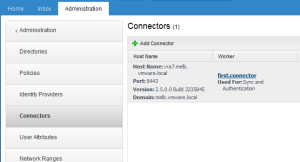
- Go to the Connectors menu, and click on the worker hyperlink (first.connector in the image below).
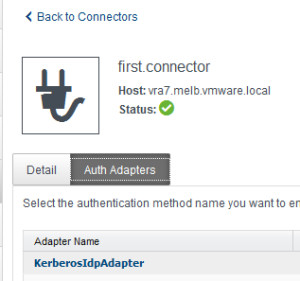
- Select the Auth Adapters tab, and then click on KerberosIdpAdapter.
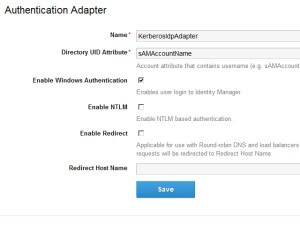
- Add the Directory UID attribute as prompted, and check the box to Enable Windows Authentication. Don’t forget to click save.
- Head to the Policies tab, and open up the default_access_policy_set. On the Web Browser line, click the hyperlinked value password under Authentication Method. Change the first method to Kerberos, and set the fallback to password and click save.
That’s it for vRA…. all you need to do now is ensure that your browser is configured to pass through your credentials and you are good to go.
Real single sign on is within your grasp. Make it happen!